Why run this assessment?

Safe,
non-invasive test runs in seconds
Uncover
risks and vulnerabilities
Learn how
to improve your ransomware risk posture
Ransomware Attack Chain
Attacker
Initial Compromise
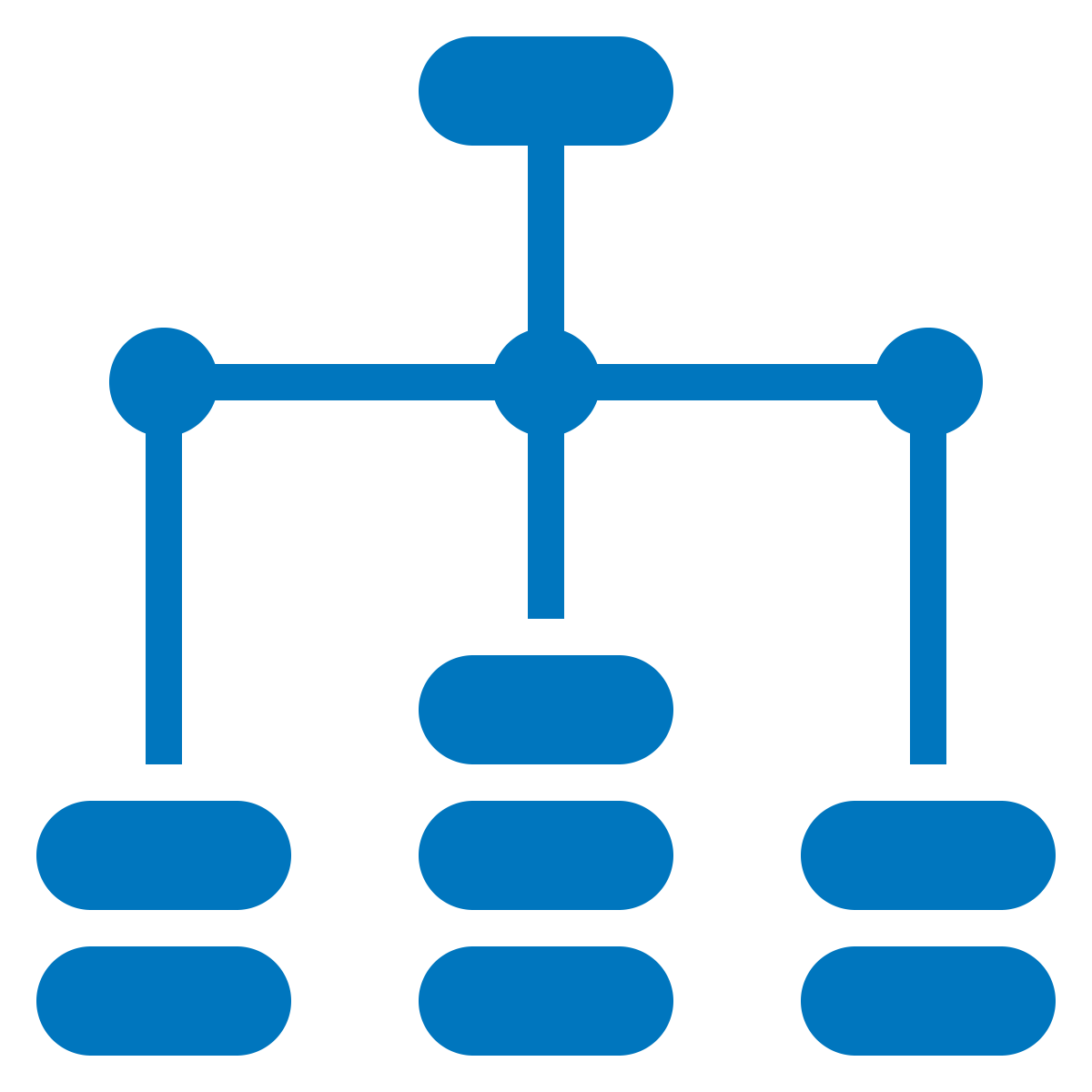
Lateral Movement
Data Loss/Exfiltration

Ransomware
Execution and Data Encryption
Initial Compromise
The first thing an attacker
must do is gain entry into a system, often by tricking a user into
downloading an infected file or clicking a malicious link. Your
first line of defense is to block these actions.
Lateral Movement
Once an attacker is in your
system, they attempt to move around the network to cause damage or
steal valuable assets. Many legacy security tools allow broad
access to valuable assets once an attacker gets in.
Data Loss/Exfiltration
Many attacks include data
theft, such as PII, financial data, or intellectual property. Your
security controls must recognise and stop attempts to steal
valuable data.